NSE scripts are written in the Lua scripting language and named with the extension . nse. They are stored in the scripts subdirectory of the main Nmap directory.
What language are NSE scripts written?
NSE scripts are written in a programming language called Lua.
What is NSE in Linux?
One of the interesting features of Nmap is the Nmap Script Engine (NSE), which brings even more flexibility and efficiency to it. … It enables you to write your own scripts in Lua programming language, and possibly share these scripts with other Nmap users out there.
What are the script types and phases of NSE?
Script categoryDescriptiondosScripts related to denial-of-service attacks.exploitScripts used to exploit security vulnerabilities.externalThis category is for scripts depending on a third-party service.fuzzerNSE scripts focused on fuzzing.What is a script scan?
The script scanner operates as a proxy component to the real Windows scripting host component. It intercepts scripts, then scans them before they are executed. If the script is clean, it is passed on to the real scripting host component. …
Where is nmap directory?
Nmap scripts are stored in a scripts subdirectory of the Nmap data directory by default (see Chapter 14, Understanding and Customizing Nmap Data Files). For efficiency, scripts are indexed in a database stored in scripts/script. db , which lists the category or categories in which each script belongs.
What is Nmap Zenmap?
Zenmap is the Nmap security scanner graphical user interface and provides for hundreds of options. It lets users do things like save scans and compare them, view network topology maps, view displays of ports running on a host or all hosts on a network, and store scans in a searchable database.
How many nmap scripts are there?
For example, Nmap includes more than 15 http service scripts to run against web servers. If a host has web servers running on multiple ports, those scripts may run multiple times (one for each port).What is nmap option?
Nmap is a network mapper that has emerged as one of the most popular, free network discovery tools on the market. Nmap is now one of the core tools used by network administrators to map their networks.
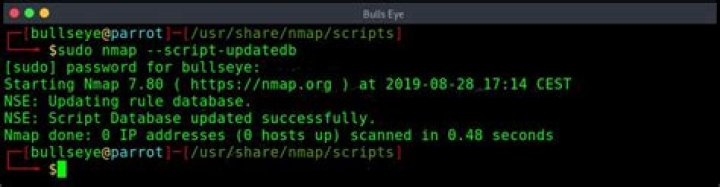
How do I add a script to nmap?- Step 1: Figure out where your scripts are stored. First, you have to find out where your scripts are installed. …
- Step 2: Get the script + libraries. …
- Step 3: Update script database (optional) …
- Step 4: Run it! …
- 6 thoughts on “How-to: install an Nmap script”
What is nmap SC?
Performs a script scan using the default set of scripts. It is equivalent to –script=default. Some of the scripts in this category are considered intrusive and should not be run against a target network without permission.
Can I use Nmap in Windows?
NMAP (Network Mapper), one of the famous open-source tools to perform network scans, security auditing, and find vulnerabilities in network infrastructure. One of the popular know usages of NMAP is to find the open ports in the network. NMAP can be installed on Windows, Linux, macOS, and much more.
Where are Nmap scripts in Kali?
“usr/share/nmap/scripts/” is where the Nmap scripts are located in the Kali Linux by default. Navigate to the folder where the scripts are located using the “cd” command. Let’s look at the script. db file first, which is a script database used by Nmap which is in the folder called the “script.
How use Nmap in Kali Linux?
- Syntax for scanning a single IP. Syntax: nmap <ip address> …
- Syntax for scanning a host. Syntax: nmap <host name> …
- Scanning a range of IPs. Syntax: …
- Scanning a single port. Syntax: …
- Scanning range of ports. Syntax: …
- Scanning 100 most common ports. Syntax: …
- Scan using TCP SYN scan.
Why do hackers use nmap?
Nmap can be used by hackers to gain access to uncontrolled ports on a system. … IT security companies often use it as a way to replicate the kinds of attacks that a system could potentially face.
What is an Nmap switch?
This switch lets you specify single ports, ranges, or lists of ports to scan. You can also specify whether you want to ping UDP or TCP ports only. For example, to scan TCP ports 23 (Telnet), 25 (SMTP), and 80 (HTTP), you can type this: NMap -p T:23,25,80.
How do I get nmap?
- Step 1: Update Ubuntu Package List. Make sure the software packages on your Ubuntu system are up-to-date with the command: sudo apt-get update. …
- Step 2: Install Nmap. To install NMAP on Ubuntu, run the command: sudo apt-get install nmap. …
- Step 3: Verify Nmap Version Installed.
Is it safe to use Nmap?
NMap is as safe as about any other well-respected free software. Nothing is totally safe. Even Windows and builds of Linux contain at best occasional vulnerabilities. There might be some restricted environments where it is against some rule to install it, but that’s a matter of policy you would need to check locally.
Is Zenmap good?
“Zenmap is best” One of the best tools for port scanning and discover hosts and their services. It is available freely in many platforms such as Windows, Linux, Mac OS X. One of the great features is frequently using commands can be saved. Filters can be added easily.
Is Zenmap better than Nmap?
Zenmap is not meant to replace Nmap, but to make it more useful. … interactive and graphical results viewing – Zenmap can display Nmap’s normal output, but you can also arrange its display to show all ports on a host or all hosts running a particular service.
Is Nmap illegal?
While civil and (especially) criminal court cases are the nightmare scenario for Nmap users, these are very rare. After all, no United States federal laws explicitly criminalize port scanning. … Unauthorized port scanning, for any reason, is strictly prohibited.
What are the benefits of Nmap?
- It can be used for auditing the Network system as it can detect the new servers.
- It can search subdomain and Domain Name system queries.
- With the help of the Nmap scripting engine (NSE), interaction can be made with the target host.
What are the 5 different output formats available in Nmap?
Those subfields are: Port number , State , Protocol , Owner , Service , SunRPC info , and Version info . As with XML output, this man page does not allow for documenting the entire format. A more detailed look at the Nmap grepable output format is available in the section called “Grepable Output ( -oG )”.
Can Nmap NSE be used to exploit vulnerabilities?
As a general scripting language, NSE can even be used to exploit vulnerabilities rather than just find them. The capability to add custom exploit scripts may be valuable for some people (particularly penetration testers), though they aren’t planning to turn Nmap into an exploitation framework such as Metasploit.
What are flags in Nmap?
Nmap flags are the parameters we use after calling the program, for example -Pn (no ping) is the flag or parameter to prevent nmap from pinging targets. Below you’ll find nmap’s main flags with examples. -p: the -p flag or parameter is useful to specify one or many ports or port ranges.
Does Nmap scan all ports?
By default, Nmap scans the 1,000 most popular ports of each protocol it is asked to scan. Alternatively, you can specify the -F (fast) option to scan only the 100 most common ports in each protocol or –top-ports to specify an arbitrary number of ports to scan.
Why does Nmap take so long?
By default, Nmap scans the most common 1,000 ports. On a fast network of responsive machines, this may take a fraction of a second per host. But Nmap must slow down dramatically when it encounters rate limiting or firewalls that drop probe packets without responding. UDP scans can be agonizingly slow for these reasons.
How about if I want to scan every port?
Scan All TCP Ports with Range We can specify the port range with the -p option. As we know TCP port numbers are between and 65535 . We will use -p0-65535 as an option in order to scan all TCP ports. We do not specify the TCP protocol because the default protocol for Nmap port scan is TCP.
How do I run a Nmap scan?
- Download the installer.
- Run the installer.
- Open NMap/Zenmap.
- Enter the target address.
- Choose a profile.
- Click Scan.
- Review the results.
What is tenable Nessus?
Nessus is a remote security scanning tool, which scans a computer and raises an alert if it discovers any vulnerabilities that malicious hackers could use to gain access to any computer you have connected to a network.
What is the use of SMB-OS-discovery NSE script?
Script Description The smb-os-discovery. nse script attempts to determine the operating system, computer name, domain, workgroup, and current time over the SMB protocol (ports 445 or 139).