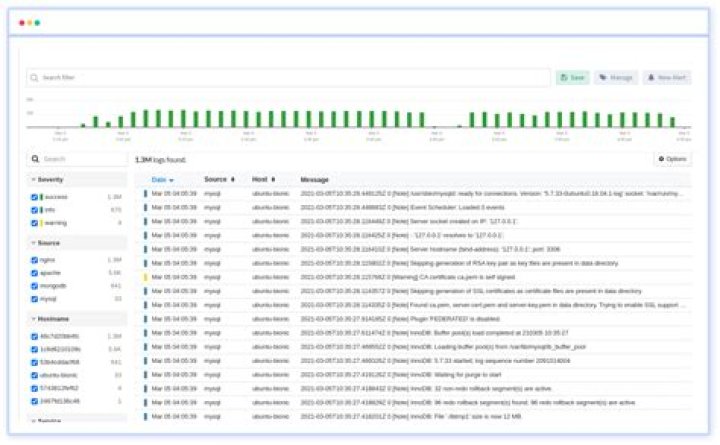
Sematext Logs.SolarWinds Loggly.Splunk.Logentries (now Rapid7 InsightOps)logz.io.Sumo Logic.SolarWinds Log & Event Manager (now Security Event Manager)ManageEngine EventLog Analyzer.
Which of the following tool is a log analysis?
ManageEngine EventLog Analyzer (FREE TRIAL) Comprehensive event monitor for Windows Server and Linux. Loggly (FREE TRIAL) Online log consolidator with great analysis tools. Sematext Logs (FREE TRIAL) A cloud-based log management and analysis service that provides system performance and security data.
What is log analysis used for?
Log analysis is the process of reviewing computer-generated event logs to proactively identify bugs, security threats, factors affecting system or application performance, or other risks. Log analysis can also be used more broadly to ensure compliance with regulations or review user behavior.
What tools can be used for log collection?
- SolarWinds Kiwi Syslog Server (Free Trial)
- ManageEngine EventLog Analyzer.
- Syslog-ng Store Box.
- Graylog.
- NXLog.
How do you Analyse firewall logs?
- Look for probes to ports that have no application services running on them. …
- Look at the IP addresses that are being rejected and dropped. …
- Look for unsuccessful logins to your firewall or to other mission-critical servers that it protects. …
- Look for suspicious outbound connections.
How do you manage logs?
- Set a Strategy. Don’t log blindly. …
- Structure Your Log Data. …
- Separate and Centralize your Log Data. …
- Practice End-to-End Logging. …
- Correlate Data Sources. …
- Use Unique Identifiers. …
- Add Context. …
- Perform Real-Time Monitoring.
How do you monitor logs?
- tail Command – Monitor Logs in Real Time. …
- Multitail Command – Monitor Multiple Log Files in Real Time. …
- lnav Command – Monitor Multiple Log Files in Real Time. …
- less Command – Display Real Time Output of Log Files.
How do I analyze server logs?
- IP Address and host name.
- Country or region of origin.
- Browser and operating system used.
- Direct access by the user or reference from another website or advertising measure.
- Type of search engine and search term entered.
- Duration and number of pages visited by the user.
What is a log monitoring tool?
Log monitoring is a practice used by IT administrators to organize, analyze, and understand a network’s performance. All network devices, including applications and hardware, create logs as they perform operations.
What is log monitoring and analysis?Log monitoring is the act of reviewing collected logs as they are recorded. … Log analysis, on the other hand, is a process typically performed by developers or other IT folks within an organization for various reasons — often related to troubleshooting issues within a system or application.
Article first time published onWhich one is log visualization tool in Microservices?
Loggly. This is a popular log analysis and monitoring solution that is adept at logging data from Docker containers. The data captured by Loggly can be used to monitor, analyze and optimize microservices-based applications.
What is log management system?
Log management systems provide a commercial solution for log collection, analysis, and reporting. Log management systems provide a configuration interface to manage log collection, as well as options for the storage of logs—often allowing the administrator to configure log retention parameters by individual log source.
Which of the following tool is used for monitoring and logging?
1. SolarWinds Papertrail. SolarWinds® Papertrail™ is a hosted log management tool designed to help you collect and monitor logs from your servers, applications, databases, networking devices, syslog, cloud, and more.
Which tools can be used for logging in Microservices architecture?
There are various tools to do that. The most popular ones are Logstash and Fluentd. For example, if you orchestrate your microservices with containers by using k8s, both of them have an implementation(Filebeat/Fluentbit) to collect logs from the containers.
Why is it important to perform log analysis in a network?
Log analysis is an important function for monitoring and alerting, security policy compliance, auditing and regulatory compliance, security incident response and even forensic investigations.
How log analysis can be used for evaluating digital library?
Log analysis is an effective approach to illustrate usage patterns, in particular how users interact with digital libraries. Digital libraries were not frequently used compared with other types of online resources, especially in the early age of digital library development.
How do logs assist a cyber security analyst?
In relation to cyber security, log data points out to the red flags in your systems: unusual behaviour, unauthorized access, extreme traffic, suspicious changes and such. Through log monitoring, you can detect malicious attacks and threats.
What is the best firewall for detailed logging?
- Cisco ASA Device.
- CyberGuard.
- Fortigate.
- Microsoft ISA.
- NetScreen.
- SonicWALL.
- WatchGuard.
- and many others.
What is firewall analysis tools?
Firewall Analyzer helps you assess the impact of network security policies on traffic, troubleshoot connectivity issues, plan changes and perform “what-if” traffic queries.
Why is log analysis important to safeguarding your firewall and network?
Being on top of logs means a quicker response time to security events and better security program effectiveness. Not only will log analysis and daily monitoring demonstrate your willingness to comply with PCI DSS and HIPAA requirements, it will also help you defend against insider and outsider threats.
How do I Analyse log files in Linux?
One of the simplest ways to analyze logs is by performing plain text searches using grep. grep is a command line tool that can search for matching text in a file, or in output from other commands. It’s included by default in most Linux distributions and is also available for Windows and Mac.
How do I check system logs in Ubuntu?
- Authorization log. Location: /var/log/auth.log. …
- Daemon Log. Location: /var/log/daemon.log. …
- Debug log. Location: /var/log/debug. …
- Kernel log. Location: /var/log/kern.log. …
- System log. Location: /var/log/syslog. …
- Apache logs. Location: /var/log/apache2/ (subdirectory) …
- X11 server logs. …
- Login failures log.
How do I check system logs in Linux?
Linux logs will display with the command cd/var/log. Then, you can type ls to see the logs stored under this directory. One of the most important logs to view is the syslog, which logs everything but auth-related messages.
What is a log management database?
Log management databases are special cases of time-series databases. The information arrives in a steady stream of ordered events, and the log files record them.
What is a log in computing?
A log file is a computer-generated data file that contains information about usage patterns, activities, and operations within an operating system, application, server or another device.
What is azure monitor logs?
Azure Monitor Logs is a feature of Azure Monitor that collects and organizes log and performance data from monitored resources. Data from multiple sources can be consolidated into a single workspace.
What is Splunk tool?
Splunk is a software platform widely used for monitoring, searching, analyzing and visualizing the machine-generated data in real time. It performs capturing, indexing, and correlating the real time data in a searchable container and produces graphs, alerts, dashboards and visualizations.
What are logging tools in DevOps?
- Papertrail: Papertrail is a centralized log management tool that helps in tracking down customer problems, error messages, and application requests. …
- Scalyr: …
- Logz.io: …
- Fluentd: …
- TIBCO LogLogic: …
- vRealize Log Insight: …
- Sentry: …
- Logstash:
How do I read a log file?
You can read a LOG file with any text editor, like Windows Notepad. You might be able to open one in your web browser, too. Just drag it directly into the browser window, or use the Ctrl+O keyboard shortcut to open a dialog box to browse for the file.
What is log analysis UX?
Analysis of site-search logs is one of the biggest missed opportunities in UX research. … That’s the outside view of your search traffic that shows which terms and websites drive traffic to your site.
What is log analysis in Linux?
Linux logs are an important tool for developers, network admins, and security professionals alike. They document a timeline of events that occur on a Linux system, including operating system events, application activity, and user actions. These logs are stored in the /var/log directory.