The first step in securing an API is to ensure that you only accept queries sent over a secure channel, like TLS (formerly known as SSL). Communicating with a TLS certificate protects all access credentials and API data in transit using end-to-end encryption. API keys are another step toward securing a REST API.
How do I secure Web API?
Securing your API against the attacks outlined above should be based on: Authentication – Determining the identity of an end user. In a REST API, basic authentication can be implemented using the TLS protocol, but OAuth 2 and OpenID Connect are more secure alternatives.
How do I protect my private API?
You can protect your API using strategies like generating SSL certificates, configuring a web application firewall, setting throttling targets, and only allowing access to your API from a Virtual Private Cloud (VPC).
How do you build an API security?
- Use tokens. Establish trusted identities and then control access to services and resources by using tokens assigned to those identities.
- Use encryption and signatures. …
- Identify vulnerabilities. …
- Use quotas and throttling. …
- Use an API gateway.
How do I make REST API more secure?
- 2.1. Keep it Simple. Secure an API/System – just how secure it needs to be. …
- 2.2. Always Use HTTPS. …
- 2.3. Use Password Hash. …
- 2.4. Never expose information on URLs. …
- 2.5. Consider OAuth. …
- 2.6. Consider Adding Timestamp in Request. …
- 2.7. Input Parameter Validation.
How do I encrypt a Web API response?
- Type some text and select “Encrypt”. Click on the “Submit” button. It generates an encrypted code version of the text.
- Copy the encrypted code and paste it into the text box and select decrypt. Now click on the “Submit” button. It generates the original text.
How do I secure my API key?
- Do not embed API keys directly in code. …
- Do not store API keys in files inside your application’s source tree. …
- Set up application and API key restrictions. …
- Delete unneeded API keys to minimize exposure to attacks.
- Regenerate your API keys periodically.
How can I secure my backend?
- Implement multi-factor authentication to prevent automated attacks.
- Encourage (or force) the user to adopt a good password policy.
- Limit failed logins.
- Use efficient algorithm hash.
How can you secure your API in MuleSoft?
Anypoint API Manager The third option is to use an out-of-the-box component within MuleSoft’s Anypoint Platform — the API Manager. It basically creates an API Proxy for each backend API running on Anypoint Platform and thereby secures requests coming into the platform again the API.
Which is the most secure method to transmit an API key?HMAC Authentication is common for securing public APIs whereas Digital Signature is suitable for server-to-server two way communication. OAuth on the other hand is useful when you need to restrict parts of your API to authenticated users only.
Article first time published onHow do I secure API gateway?
- Serving as an inline proxy point of control over APIs.
- Verifying the identity associated with API requests through credential and token validation, as well as other authentication means.
- Determining which traffic is authorized to pass through the API to backend services.
How do I secure my API token?
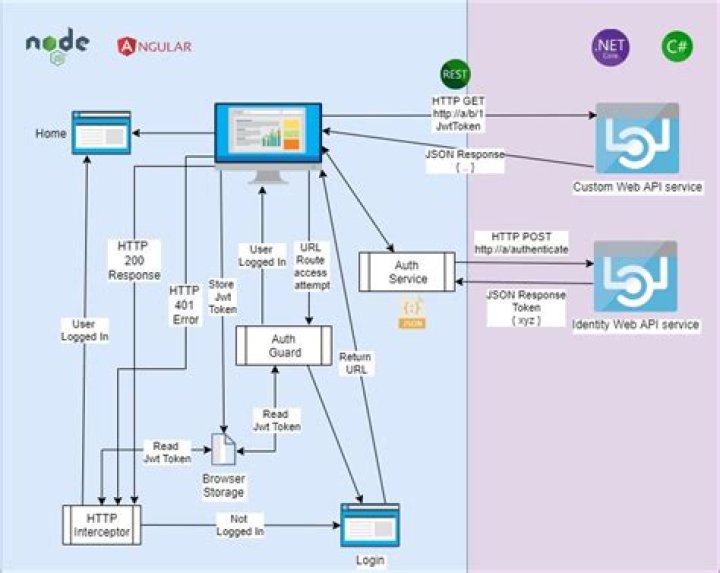
- The user/client app sends a sign-in request. …
- Once verified, the API will create a JSON Web Token (more on this in a bit) and sign it using a secret key.
- Then the API will return that token back to the client application.
How do I restrict access to API?
- Grant permission to enable the API.
- Create a separate Google Cloud project for each caller.
- Create an API key for each caller.
- Create one API key for all callers.
How does Web API authorization work?
Web API uses authorization filters to implement authorization. The Authorization filters run before the controller action. If the request is not authorized, the filter returns an error response, and the action is not invoked. Web API provides a built-in authorization filter, Authorize Attribute.
How do I authenticate and authorize in Web API?
Web API provides a built-in authorization filter, AuthorizeAttribute. This filter checks whether the user is authenticated. If not, it returns HTTP status code 401 (Unauthorized), without invoking the action. You can apply the filter globally, at the controller level, or at the level of individual actions.
How do I create a secure REST API in spring boot?
- Secure Your Spring REST API with OAuth 2.0.
- Add a Resource Server Your Spring REST API.
- Set Up an OAuth 2.0 Resource Server.
- Add Spring Security to Your REST API.
- Generate Tokens in Your Spring REST API.
- Add OAuth 2.0 Scopes.
How do I create my own API key?
- Go to the API Console.
- From the projects list, select a project or create a new one.
- If the APIs & services page isn’t already open, open the left side menu and select APIs & services.
- On the left, choose Credentials.
- Click Create credentials and then select API key.
Do API keys need to be encrypted?
API keys are normally used for identification and authentication, not encryption. The client includes them in requests, so the server can figure out which client is making the request and be confident the call is really coming from that client.
What is an API key secret?
The API Key and API Key Secret are essentially software-level credentials that allow a program to access your account without the need for providing your actual username and password to the software. … These values can be used to access all of your account data and should be treated the same as a username and password.
Can API be intercepted?
Logging request URLs Here we use onBeforeRequest to call the logURL() function just before starting the request. The logURL() function grabs the URL of the request from the event object and logs it to the browser console. The {urls: [“<all_urls>”]} pattern means we will intercept HTTP requests to all URLs.
Are RESTful Web Services Secure?
About RESTful Web Service Security You can secure your RESTful Web services using one of the following methods to support authentication, authorization, or encryption: Updating the web. xml deployment descriptor to define security configuration. See Securing RESTful Web Services Using web.
What does TLS use for encryption?
TLS uses symmetric-key encryption to provide confidentiality to the data that it transmits. Unlike public-key encryption, just one key is used in both the encryption and decryption processes. Once data has been encrypted with an algorithm, it will appear as a jumble of ciphertext.
What is API gateway security?
API Gateway Security – What is an API Gateway? The API Gateway is an important part of an API solution. API Gateways enforce policies which control security aspects such as the authentication, authorization or traffic management. The API Gateway is comparable to a gatekeeper guarding the underlying data.
What is the difference between apigee and Mulesoft?
Apigee is more mature in microservice management, while Mulesoft is ahead in integration capabilities. Both companies are working to close these gaps – see Mulesoft’s October 2019 release and Google’s Anthos platform – so prospective clients will soon need to look even deeper to find differentiation between the two.
Is API gateway same as API management?
Here, we make our first distinction between API management and API gateways. An API gateway is a component or tool of an API management approach. Gateways are used as the entry point for client requests. This allows them to facilitate requests, combine results, and handle things like authentication.
What is backend security?
We know that backend security is important, but what exactly constitutes the “backend?” To put it simply, the backend is the portion of a website, web application, or mobile application that exists behind the scenes. By contrast, the “frontend” of an application is everything that the user interacts with.
Which are most likely back end server side threats?
- Data Injection. …
- Access Control Misconfigurations. …
- Software Misconfigurations. …
- Lack of Authentication. …
- Outdated Software Components. …
- Sensitive Data Exposure. …
- Lack of Vulnerability Scanning.
When did oauth2 come out?
OAuth 2.0 was published as RFC 6749 and the Bearer Token Usage as RFC 6750, both standards track Requests for Comments, in October 2012.
How do I authenticate API?
You can authenticate API requests using basic authentication with your email address and password, with your email address and an API token, or with an OAuth access token. All methods of authentication set the authorization header differently. Credentials sent in the payload (body) or URL are not processed.
How do I send an API key?
- HTTP Basic Authentication header.
- URL query string parameter.
- Request body field.
How do I protect API gateway with API key?
The steps to enable security using API-Keys are: Share the generated API-Key (either manually or via AWS Developer portal) with the API consumers. API consumers then sends the API-Key as a HTTP header in the API request. AWS API Gateway checks the header and compares it with the key associated with the API.